You need a complex system of security and reporting systems in place to ensure the safety and integrity of your physical infrastructure and the digital data youmr company keeps. You must also gather human, technological, and quantitative cybersecurity metric resources to assess the effectiveness of your defenses. Without these tools, no security posture is complete. So, here are some cybersecurity metrics that may and should be tracked to guarantee that your security efforts are as efficient as possible.
Why are cybersecurity and data security metrics important?
Security monitoring is a continuous process, not a one-time event. The technology that has to be safeguarded, as well as the threats that jeopardize it, are always changing. As a result, you should have procedures in place to evaluate the efficiency of the precautions you’ve put in place on a regular basis.
You may get a snapshot of how your security system is performing over time by analyzing key performance indicators (KPIs) and key risk indicators (KRIs). You can make decisions regarding your security future using this data.
One of the greatest methods to be accountable to all stakeholders is to identify and use these information security metrics examples in monitoring your ongoing network protection protocols.
Cybersecurity KPIs to track
Level of preparedness
How many of your network’s devices are patched and up to date? One of the 20 CIS Controls that might reduce the risk of vulnerability exploits is vulnerability scanning and management.
Unidentified devices on internal networks
When employees bring in their own devices, as well as improperly configured Internet of Things (IoT) devices, they might introduce malware and other cyber risks, which is why network intrusion detection systems are a crucial aspect of your organization’s security.
Intrusion attempts
Attempts at the intrusion, both successful and unsuccessful. How many times have dishonest actors tried to obtain unauthorized access to your system?
Number of Security incidents
How many times has an attacker gained access to your data or networks?
Mean Time to Detect (MTTD)
How long does it take for a security threat to go unnoticed? The time it takes for your team to become aware of indicators of compromise and other security issues is measured in MTTD.
Mean Time to Resolve (MTTR)
What is your team’s average response time to a cyber assault once they become aware of it? A good indicator of how well your incident response plan is being implemented. Adopting react best practices in your development process can contribute to the overall security of your systems, just as monitoring cybersecurity metrics does.
Mean Time to Contain (MTTC)
Meantime to detect (MTTI) and mean time to contain (MTTC) are cybersecurity metrics and statistics that refer to how quickly your company detects and responds to an issue. Your organization loses money when these two key performance indicators (KPIs) are too high because your team takes too long to uncover or react to attack vectors. These security KPIs should be at the top of the priority list for management.
Number of systems with known vulnerabilities
A crucial cybersecurity indicator for measuring the risk that your company faces is the number of exposed assets in your environment. Managing updates and patches is a time-consuming procedure, but it’s critical to avoid security flaws in your environment. A vulnerability scan that covers all assets will reveal what has to be done to improve your company’s security posture. A vulnerability management program is more than a nicety; it’s a requirement.
Number of SSL certificates configured incorrectly
An SSL certificate is a file that verifies the website or company with which data is being transferred as the owner of a cryptographic key, ensuring the transaction’s legitimacy. Monitoring each certificate’s security requirements and ensuring that they are correctly configured on servers protects them from falling into the wrong hands and your company’s digital identity from being used to steal user information. It is essential to purchase an SSL certificate before the data comes at a risk.
Days for security patch implementation
How long does it take your team to apply security updates or patch CVE-listed vulnerabilities that are considered high-risk? Threat intelligence technologies are frequently used by cybercriminals, who take advantage of the time between patch release and installation.
Number of users with admin access level
Full control of users’ level of access to company resources is a best practice in information security management; an employee should only have access to data, systems, and assets that are required for their job. By identifying all network users’ access permissions, you can alter them as appropriate, such as barring any superuser or administrator who doesn’t make sense.
When it comes to protecting your systems, it’s critical to limit who has administrative access to sensitive data. Make certain that permissions are only given as needed and that they may be canceled if the circumstance changes.
Cybersecurity awareness training results
Humans and technology must collaborate to detect and respond to dangers like phishing attempts, according to 93 percent of cybersecurity specialists. An investment in security awareness and training from reputable cybersecurity companies has a 72 percent likelihood of lowering the financial impact of a cyber assault.
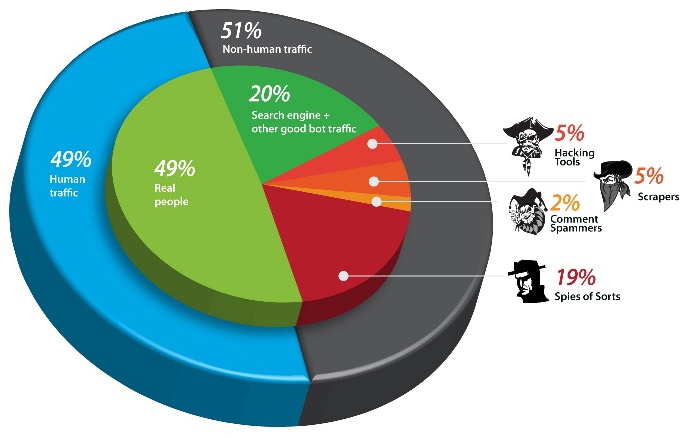
Non-human traffic (NHT)
Is the amount of visitors on your website normal, or is there an increase that could indicate a bot attack?
Virus infection monitoring
How often does your antivirus software check for known malware in common applications like email clients, web browsers, and instant messaging software?
Phishing attack success
What percentage of phishing emails do your staff actually open?
To strengthen outgoing email security and secure your domain and data, you must implement email authentication using DMARC, DKIM, and SPF. You should use an SPF record to protect your email. Domain owners can publish a list of IP addresses or subnets that are authorized to send emails on their behalf using Sender Policy Framework (SPF). You can check a domain’s records with SPF record checker to make sure everything is safe and in order. The goal is to eliminate spam and fraud by making it much harder for spammers to conceal their identities.
Cost per incident
What is the cost of responding to and resolving an attack? How much do you spend on employee overtime, investigation costs, employee productivity loss, and customer communication?
Data security and regulatory complaint metrics to track
There are several industry standards for data privacy and protection that aim at protecting both the client and the service provider from threats.
PCI DSS
PCI DSS compliance (Payment Card Industry Data Security Standard) refers to the rules and guidelines that a company must follow in order to protect its customers’ credit card information.
HIPAA
The Health Insurance Portability and Accountability Act of 1996, or HIPAA compliance, was enacted to preserve patient privacy. Setting security goals that show an organization’s attempts to meet industry best practices, standards, and regulations is critical. In fact, that’s one of the benefits of ISO 27001 compliance, as it’s often used by healthcare organizations to effectively guarantee that their data security practices are aligned with the parallel expectations laid out by HIPAA. It’s an example of how many regulations overlap in their aims and end results, so compliance can be efficient as well as fundamentally secure.
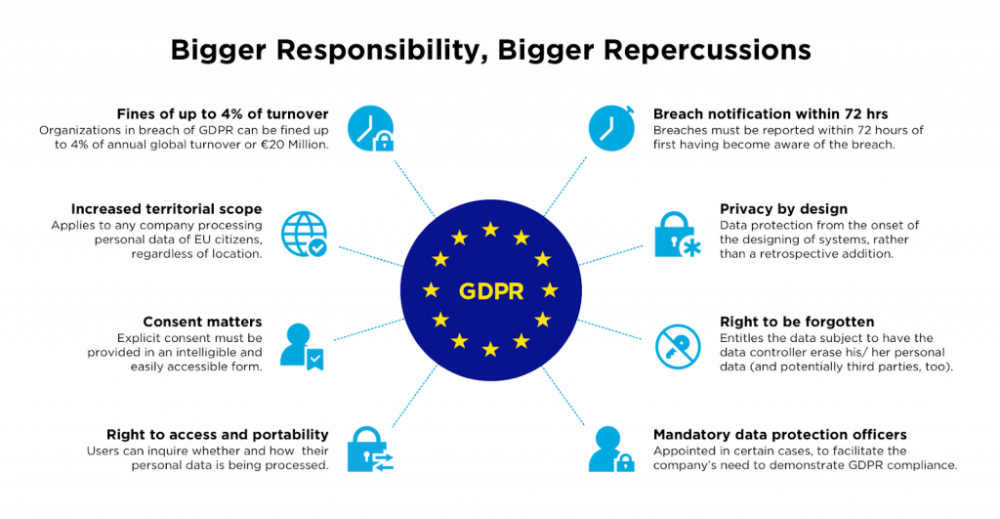
GDPR
GDPR is a recent European Union data protection law that applies to any business that handles data belonging to EU residents, even if that business is not based in the EU. Its goal is to provide people more control and transparency over their personal information. If your company is found to be non-compliant, it might face fines of up to 4% of annual turnover, as well as being removed from the market.
CPS 234
CPS 234 is an APRA Prudential Standard that aims to ensure that an APRA-regulated entity takes measures to be resilient against information security incidents (including cyber-attacks) by maintaining an information security capability that is commensurate with the vulnerabilities and threats to information security.
It applies to all APRA-regulated organizations, and non-compliance with CPS 234 can result in the loss of an RSE license.
PIPEDA
For private-sector enterprises in Canada, the Personal Information Protection and Electronic Documents Act (PIPEDA) is the federal privacy legislation.
PIPEDA was passed on April 13, 2000, with the goal of promoting trust and data privacy in e-commerce. Since then, it has expanded to encompass areas such as banking, broadcasting, and health care.
GLBA
The Gramm-Leach-Bliley Act (GLBA) is a US federal law that compels financial organizations to explain how they share and preserve nonpublic personal information about their customers (NPI).
The GLBA is made up of three primary components that work together to govern the acquisition, disclosure, and protection of nonpublic personal information (NPI) of customers:
The Financial Privacy Rule: Limits the sharing of nonpublic personal information (NPI) about individuals and requires financial institutions to give each client a privacy notice at the beginning of the customer relationship and annually thereafter.
The Safeguards Rule: Requires financial institutions to produce an information security plan that explains how they are prepared for and plan to secure nonpublic personal information of current and former customers (NPI).
Pretexting or social engineering is when someone tries to get access to nonpublic personal information without having the authority to do so. This could include impersonating the account holder over the phone, in the mail, or by phishing or spear phishing. The GLBA advises businesses to put in place precautions against pretexting.
FISMA
The Federal Information Security Management Act of 2002 (FISMA) is a federal law in the United States that establishes a comprehensive framework to safeguard government information, operations, and assets from natural and man-made threats.
The National Institute of Standards and Technology (NIST) has published standards and guidelines such as FIPS 199 Standards for Security Categorization of Federal Information and Information Systems, FIPS 200 Minimum Security Requirements for Federal Information and Information Systems, and the NIST 800 series, which further define the framework.
FISMA requires federal agencies to establish, document, and execute an agency-wide information system to support their operations and assets, including those provided or
How to choose the right cybersecurity metrics?
These seven principles will assist you in selecting the appropriate security metrics for your company:
- Metrics should support company goals and regulatory needs; linking metrics to the business can help with stakeholder buy-in and resource efficiency.
- Controllability: Metrics must show that a goal has been attained in order to be useful. As a result, metrics must assess processes and results that can be controlled.
- Context: Respond to queries such as “why are we collecting it?” “what story does it tell?” and “how does this compare to our industry?”
- Best practices: Know what you’re aiming for and what constitutes a best-in-class statistic.
- Metrics must be measurable in order to be compared across time and between businesses. As a result, the qualitative context surrounding objective key results (OKRs) is critical.
- Data quality: Metrics are only as good as the data that goes into creating them, so make sure it’s accurate, precise, and dependable.
- Ease of collection and analysis: Even the best statistic is useless if the data is difficult to obtain and interpret. Preparing and reporting your metrics shouldn’t take too long. Ideally, you should have a dashboard that is always up to date and accessible to everybody in your company.
Conclusion
Following these guidelines will assist you in identifying the data and services required to construct the metrics you require. It’s vital to realize that the data collected to construct your security metrics are influenced by your company environment. These figures will also be influenced by the technology you utilize, the security controls you employ, and the number of third-party providers you use.