While living in a highly tech-driven age, it’s important for your business to stay on top of trends but also to safeguard your digital assets.
In this article, let’s break down the importance of cloud connectivity and leveraging secure cloud platforms for your digital assets and content, and how your business can get started to do this right.
What is Cloud Connectivity and Security?
A subdomain of cybersecurity, cloud security refers to the set of policies, processes, and tools meant to ensure safe functionality when deploying and managing cloud-based networked systems.
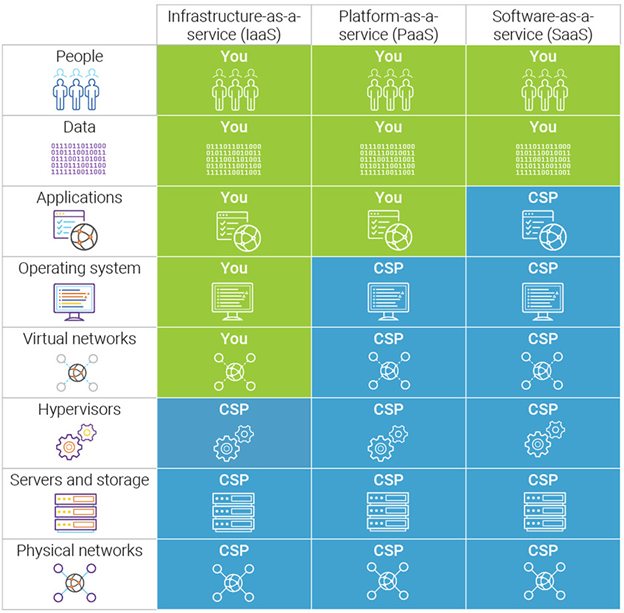
A cloud security strategy is critical to protect your business information, adhere to regulatory compliance, and ensure your customers’ data privacy. A shared responsibility between you and your cloud service provider, cloud security is meant to protect you from the reputational, financial, and legal repercussions of data breaches and data loss.
Components of Cloud Security
Cloud security is a blend of various technologies, processes, and policies, and is tailored to your individual business needs.
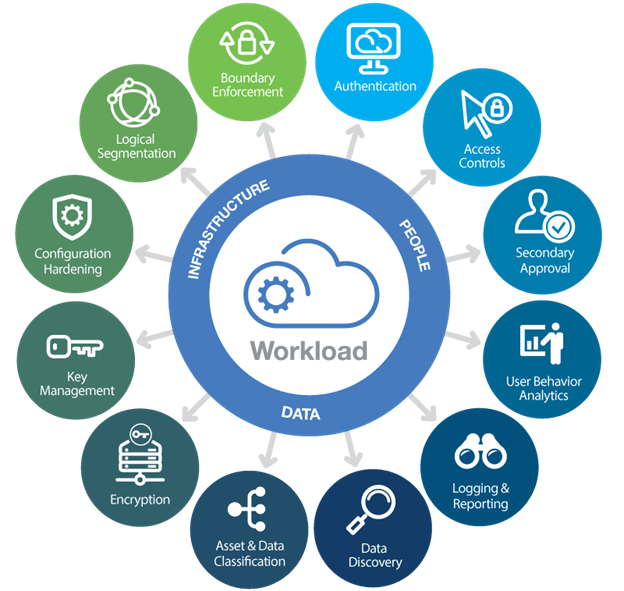
That being said, there are some tried-and-tested strategies you can use to realize a strong cloud security setup. Let’s look at them one by one.
Identity and Access Management
For starters, an Identity and Access Management (IAM) system is a must-have for your company to gain a complete understanding and visibility of each level of network access and implement access permissions accordingly.
An IAM combines multi-factor authentication and user access policies, so you (or your IT team) have total control over who has access to your information and applications, and what data they can access and alter.
Simply put, an IAM empowers your IT team to keep abreast of all connections on a network and ensure correct authentication protocols are followed.
Keep in mind that even with access control systems in place, executives and managers would do well to follow a standardized manual or guidelines for managing user access. This helps avoid mistakes, which are particularly common in large teams, and can further help in handling the complexities that come with the same.
Physical Security
The next major component of cloud security is physical security. This is to avoid disruption of the hardware housed in your cloud service provider’s data centers.
Physical security is a blend of measures to restrict direct access and avoid data loss — using high-security doors, uninterrupted power supplies, CCTV, alarms, air filtration, fire protection, and so on.
Threat Intelligence, Monitoring, and Prevention
At the heart of cloud security lie the three pillars of Threat Intelligence, Intrusion Detection Systems (IDS), and Intrusion Prevention Systems (IPS).
Threat Intelligence and IDS solutions are designed to pinpoint attackers who are currently targeting your business’s systems or might do so in the near future. IPS solutions continuously monitor your network, looking for potential malicious activities, and are meant to curb attacks and alert you so you can respond promptly.
Encryption
Encryption is a standard means to keep information secure and private during transmission over the internet. Encryption essentially conceals your data by converting it into a complex code that appears as gibberish when seen from the outside.
It is a common cybersecurity approach seen in daily activities. For example, when you shop online on Amazon, your credit card details are encrypted and made indecipherable until the data reaches the destination.
When it comes to cloud connectivity, you are transmitting data to and from the cloud provider’s platform, likely also storing it within their infrastructure. Encryption is a vital layer of cloud security to guard your information and make sure it’s near impossible to decode without a decryption key that only you possess.
Cloud Vulnerability Testing
Think about building muscle — the only way to truly improve your muscle mass and strength is to tear those tissues and test your limits, bouncing back stronger than before.
Somewhat similarly, cloud vulnerability and penetration testing involve breaching your own cloud infrastructure to figure out any weak points that could be exploited by cybercriminals. You can then work with the development and cybersecurity teams to fix these weaknesses and improve your cloud security.
Segmentation and Firewalls
Segmentation — specifically, micro-segmentation — is the process of splitting your cloud deployment into separate security segments, down to the individual workload level. In doing so, you can apply flexible security policies to minimize any damage an intruder could cause, in case they are successful in their attack.
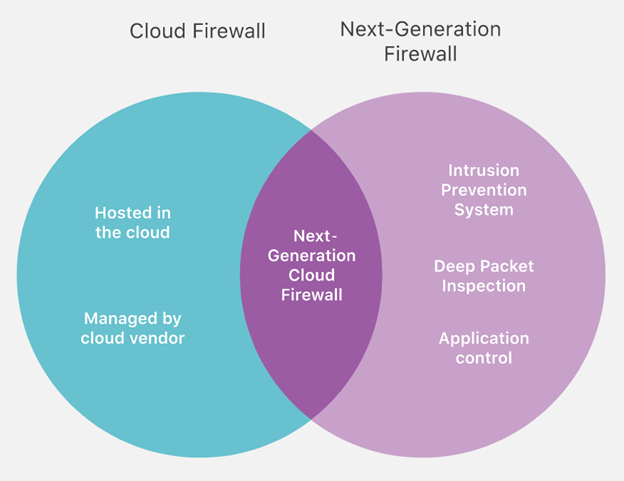
And by using next-generation firewalls, you add packet filtering, IP and port blocking, and proxying to your cloud connection, along with an intrusion prevention system, deep packet inspection, application control, and analysis of encrypted traffic to provide thorough threat detection and prevention.
Security Risks in Cloud Connectivity
When you move to the cloud, you introduce new cybersecurity risks to your business. This is not to say that cloud connectivity is insecure, as many cloud providers allow you access to amazing security tools and resources you couldn’t otherwise use.
What it means is that you must be mindful of the risks involved so you can be proactive about dodging them. Here are a few security risks in cloud connectivity you must pay heed to.
Losing Visibility
It’s likely your company will access a variety of cloud services via multiple devices and locations. Without the right tools in place, you can easily lose visibility of access to your cloud infrastructure.
That is, you wouldn’t know for sure who is using your cloud services and what data they are accessing or manipulating. So if you can’t maintain visibility, you are at a bigger risk of a data breach or loss.
Compliance Violations
Today, you are required to adhere to a range of strict compliance requirements, ranging from CCPA to GDPR. When moving to the cloud, you create a risk of compliance violations, and penalties for regulatory non-compliance can make you weep.
Many of these regulations mandate your business to know where your data is, who can access it, how it’s used, and how it’s secured. Some regulations require that your cloud provider shares certain compliance credentials too.
A reckless transfer of data to the cloud, or partnering up with the wrong provider, can make your company non-compliant — which can be a legal and financial nightmare.
Lack of Secure Architecture
An easily avoidable cloud security risk — don’t be hasty in migrating your business’s systems and data to the cloud. In doing so, you risk becoming operational before the security systems are in place to protect your cloud infrastructure.
Be sure to first have a cloud security strategy in place for your infrastructure before you go live.
Insider Threats
Current or former employees, contractors, and business partners can pose a huge security risk. Even if they don’t have a sinister intent, they can cause serious harm to your business due to lack of training or carelessness.
Most organizations already face this risk, but when you move to the cloud, you add your cloud service provider to the list of insider threat programs from the provider’s employees.
Insecure Application User Interface (API)
Cloud service providers typically rely on APIs as a way for their clients to access and fetch information from cloud-based services. If not set up properly, an external API is a doorway offering unauthorized access to cybercriminals.
Why You Need Cloud Security
With better data accessibility, convenience, and performance associated with cloud connectivity comes additional cybersecurity threats that you need to address.
The growing volume and complexity of cyber threats drive the need for cloud security. Failure to address the security risks outlined above can even put you out of business. Here are three of the many reasons why cloud security is imperative.
Cyber Security Threats Will Grow
Nearly 80% of companies experienced at least one cloud data breach between January 2019 and June 2020, with 43% reporting 10 or more data breaches.
So a major impetus for adopting secure cloud practices is the growing threat from cyber attackers — both in amount and complexity.
Preventing Data Breaches and Data Loss
To re-emphasize the previous point on data breaches, get this — over 4 billion records were exposed in the first half of 2019, according to Norton. And a data breach or loss can have dire repercussions on your company, with the average total cost of a data breach being $3.86 million.

Business Continuity and Contingency Planning
A solid cloud security strategy ensures business continuity. Unforeseen outages and system downtime can greatly impact your business’s bottom line.
Best Practices for Cloud Security
Before you move to the cloud, make sure to understand the following few best practices to maintain the security of your cloud-based systems and data.
Choose the Right Provider
First and foremost, pick a trusted cloud provider with a track record of client satisfaction — one who renders best-in-class security protocols and conforms to the highest levels of industry standards.
A trusted provider is sure to showcase their security compliance and certifications publicly. For instance, industry-leading providers like Amazon Web Services, Google Cloud, and Azure allow transparent access so you can see their security compliance and related certifications.
The right provider will also likely extend a marketplace of reliable partners and solutions to you so you can further reinforce the security of your cloud deployment.
Review Your Contracts and SLAs
In case of a data breach or loss, cloud service contracts and SLAs are the only assurance of service and recourse.
62.7% of cloud providers don’t specify whether customer data is owned by the customer, which results in an ambiguity where a provider could claim ownership of your customer data.
Check the policies regarding data ownership and what happens to the data if you end your partnership. Verify the provider’s terms on visibility into any security events and responses. Also, try to negotiate if the terms on the contract or SLA aren’t agreeable, and consider switching to an alternative if the risks seem unbearable.
Train Your Teams
As mentioned earlier, your employees can cause serious damage to your business due to a lack of cybersecurity training or negligence. But if your employees are trained well, they can immensely contribute to protecting your systems and closing the doors for potential attacks.
Creating and implementing a training program for all staff who access your cloud systems. They should know how to spot phishing in cold emails, malicious links, and the risks that come with carelessness.
This may require a shift to the culture and thinking by making security a top concern for all employees, but it’s a good change to implement.
For advanced and primary users (like admins), consider rigorous training and certification programs such as the CCSP, CCSK, etc.

Control and Monitor User Access
Complete control over user access through strict policies is a vital best practice. Admins must have total visibility of each level of network access and enforce access permissions accordingly.
Implement the zero-trust security protocol, only enabling users access to the systems and data they need to do their jobs efficiently, and nothing more.
Create clearly defined user groups with pre-assigned roles and permissions to only grant access to select information. You can then add new members directly to groups, instead of customizing access for each teammate.
Implement Encryption and Strong Passwords
Encryption is indispensable once you switch to the cloud because when you’re using cloud services, your data is constantly being sent back and forth between your network and the provider’s, and is stored on the third-party cloud platform, thus making it more vulnerable.
Make sure to go for the highest levels of data encryption both in transit and at rest.
Consider building your own encryption solutions (and keys for full control) before data transmission to the cloud as even though a cloud provider extends built-in encryption services to protect your data, it grants them access to your encryption keys.
And of course, enforcing a super-strong password policy for all users and systems goes without saying. Near-impenetrable passwords are a great first line of defense against brute-force attacks. And so, your password policy should look something like this:
- At least one upper-case and one lower-case letter
- At least one numeric character and one symbol/special character
- Minimum of 14 characters
- No use of names, dates, or any personal identifiers to aid memory
Also, implement two-factor authentication — wherein users are required to enter a verification code sent to their registered phone or email to validate their identity — to have an added layer of security.
Conclusion
If you’re on your way to becoming a fully cloud-connected business, be ready to implement a strong cloud security strategy from the outset.
Take the time to research the best cloud service provider for your business. Many cloud providers offer advanced security features along with hardware and software you wouldn’t find elsewhere.
Devise a thorough strategy that includes stringent policies, well-defined processes, and reliable tools. Understand the importance of compliance and shared responsibility of data between your business and the provider.
Ultimately, there’s no way to foolproof your business’s cloud security, but there’s a lot you can do to enhance your security stance and minimize your risks.
About the author
Mark Quadros is a Saas Content Marketer that helps brands create and distribute rad content. On a similar note, Mark loves content and contributes to several authoritative blogs like HubSpot, CoSchedule, Foundr, etc. Connect with him via LinkedIn or Twitter.
